Eliminating OT Downtime and Meeting the 2028 Quantum Deadline — Without Replacing Your Hardware
Executive Summary
When a PLC fails on your factory floor, your process stops. In heavy manufacturing and critical infrastructure, unplanned downtime costs between $50,000 and $250,000 per hour — not counting the cost of physical replacement, firmware restoration, manual state reconstruction, and the maintenance window required to bring the process back online safely. This is not a technology limitation. It is an architectural choice. The assumption baked into every Purdue-model OT deployment is that the PLC is the process: the hardware and the control logic are inseparable. VeilNet breaks that assumption.
VeilNet's self-healing PLC edge cloud architecture decouples control logic from the hardware that executes it. By encapsulating PLC programs as portable, version-controlled containers coordinated across a distributed cluster via VeilNet's proprietary Anchor Protocol, VeilNet transforms process control from a hardware-bound, single-point-of-failure discipline into a resilient, software-defined workload. When a physical node fails, control resumes automatically on available hardware within seconds, with full process state preserved. When a logic update is required, it deploys with zero process downtime. When a new site comes online, it joins the existing cluster immediately. These benefits stand entirely on their own — independent of any regulatory mandate or cryptographic consideration.
The quantum dimension adds urgency to an already compelling operational case. Nation-state adversaries are already capturing encrypted Modbus, OPC-UA, and DNP3 traffic today, with the explicit intent to decrypt it once quantum hardware matures. The Australian Signals Directorate has responded with a binding deadline: organisations must begin implementing quantum-resistant cryptography in their most critical systems by the end of 2028, with full transition mandated by 2030 under the Security of Critical Infrastructure Act 2018. For responsible officers of SOCI-registered entities, failure to meet this deadline carries personal liability exposure — not just organisational penalties. Hardware replacement to meet this deadline is physically and financially impossible. A software-defined path is the only viable option.
VeilNet delivers both outcomes from a single deployment. The same fabric that eliminates hardware-bound PLC fragility also enforces NIST-finalised post-quantum cryptographic standards across every packet, on every protocol, across every device — including hardware that has never received a firmware update and never will.
The deployment follows a deliberate three-phase progression:
Phase 0 describes the current industry-standard architecture — subnet isolation, MQTT data streaming, and perimeter firewall policies — and its structural limitations.
Phase 1 replaces the network layer entirely with a quantum-resistant, identity-authenticated overlay that eliminates public IP exposure, removes MQTT dependencies, and enables remote operation without compromising OT isolation. No changes to existing SCADA software, PLC runtimes, or IO device configuration are required.
Phase 2 replaces the control plane. PLC logic migrates into containerised workloads orchestrated across a multi-site Kubernetes cluster, enabling hot standby failover, zero-downtime logic updates, and dynamic cross-site control allocation. This phase represents a significant workflow transition and is designed to be adopted incrementally.
Operational Benefits — Independent of Quantum Compliance:
- Near-zero MTTR when a PLC host fails — control logic resumes automatically on available hardware with full process state preserved, eliminating manual replacement and restoration procedures that currently cost hours of downtime per incident
- Zero-downtime logic updates — PLC programs update via Kubernetes rolling deployments, inheriting state from their predecessor, without halting the process
- Remote operation without firewall compromise — the meta air gap enables full bidirectional remote access to OT assets without exposing any public IP or weakening subnet isolation
- Elimination of MQTT broker dependencies — direct OPC-UA streaming replaces best-effort MQTT, removing the broker as a single point of failure for process-critical telemetry
- Horizontal scaling without infrastructure redesign — new sites and nodes join the existing cluster and inherit all operational capabilities immediately, at linear not exponential cost
- Unified IT/OT observability — system-wide OpenTelemetry across both domains from a single dashboard, without firewall policy exceptions
Quantum Readiness and Regulatory Compliance:
- Zero hardware replacement required to achieve ASD 2028 quantum-readiness compliance across SOCI Act registered entities
- ML-KEM and ML-DSA enforced across all legacy OT protocols — Modbus, OPC-UA, and DNP3 become quantum-resistant without protocol-level modification
- Meta air gap isolation eliminates public IP attack surface while preserving full remote operation capability
- Sub-millisecond cryptographic overhead with no impact on existing SCADA software, PLC runtime, or IO device configuration
- Full ASD CI Fortify and SOCI Act CIRMP alignment with a direct, auditable evidence trail for regulatory audit
The Impending Regulatory Horizon and the Quantum Threat Landscape
The theoretical threat of quantum computing has rapidly materialised into an operational crisis for global critical infrastructure. Classical asymmetric algorithms — RSA, ECC, and the Diffie-Hellman variants underpinning TLS, VPNs, and OT protocol authentication — are mathematically vulnerable to Shor's algorithm running on a sufficiently capable quantum processor.
The "Harvest Now, Decrypt Later" Imperative
The quantum threat is not confined to the future. It is a present-day cybersecurity crisis. Nation-state adversaries and advanced persistent threat groups are systematically intercepting and storing encrypted OT network traffic at scale today. The data being captured includes process control telemetry, engineering workstation sessions, SCADA historian exports, and remote access streams. Once a Cryptographically Relevant Quantum Computer becomes available, this stored traffic becomes fully legible.
For critical infrastructure operators, the consequences extend beyond intellectual property loss. Decrypted historical OT traffic enables adversaries to reverse-engineer process control logic, identify physical process dependencies, and develop targeted cyberweapons calibrated to specific industrial installations — long after the initial interception occurred.
Global Regulatory Mandates and the 2028 Transition Deadline
Recognising the severity of this threat, international regulatory bodies have issued strict mandates for rapid migration to Post-Quantum Cryptography. The PQC migration timeline landscape across jurisdictions is now clearly defined, with enforceable deadlines replacing earlier aspirational guidance.
In the United States, National Security Memorandum 10 (NSM-10) and the NSA's Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) mandate that all software, firmware, and networking equipment supporting national security systems must support quantum-resistant algorithms by 2026, with all legacy systems deprecated by 2030.
In Australia, the regulatory framework is driven by the Security of Critical Infrastructure Act 2018 and explicit guidelines from the Australian Signals Directorate. Australia's preparation for post-quantum cryptography reflects the ASD's assessment that the CRQC threat timeline has materially shortened. The ASD has established a rigid PQC transition timeline for Australian critical infrastructure:
- By end of 2026: Organisations must have a refined, comprehensive PQC transition plan.
- By end of 2028: Organisations must commence active implementation of PQC algorithms, beginning with their most critical and sensitive systems — precisely the OT and ICS environments where VeilNet operates.
- By end of 2030: Organisations must complete their transition, entirely deprecating classical asymmetric algorithms.
Failure to meet the 2028 commencement deadline triggers severe regulatory penalties, mandatory incident reporting obligations, and potential personal liability for responsible officers of SOCI-registered entities under the enhanced CIRMP Rules. The ASD CI Fortify program treats PQC transition as a baseline security requirement — not a future enhancement.
Evaluating Quantum Readiness: QKD versus Software-Defined PQC
OT operators and CISOs architecting 2028 compliance strategies face two methodological options: Quantum Key Distribution and Post-Quantum Cryptography. The choice has profound operational and financial implications, and the distinction between QKD and PQC is frequently misunderstood in procurement conversations.
The Logistical and Financial Infeasibility of QKD
Quantum Key Distribution utilises the fundamental principles of quantum mechanics to establish an encryption key between two parties. Any interception attempt disturbs the quantum state and is theoretically detectable. In practice, QKD imposes constraints that make it unviable for OT environments:
Extreme Capital Expenditure: QKD cannot be implemented as a software patch. It mandates specialised photonic hardware including quantum random number generators, single-photon detectors, and dedicated dark fibre. Per-node hardware costs range from $100,000 to over $1,000,000 USD, with network operators projected to spend $6.3 billion on QKD infrastructure over the next six years — costs entirely incompatible with the OT upgrade budgets of most SOCI Act registered entities.
Distance Limitations: Discrete-Variable QKD systems achieve maximum reliable distances of approximately 100 to 150 kilometres without repeaters — ruling out distributed SCADA networks and the remote sites that characterise Australian critical infrastructure.
The Trusted Node Vulnerability: To traverse distances greater than 150 kilometres, QKD networks must utilise "trusted relay" nodes where the quantum key is converted back to classical bits — destroying the quantum security property at each relay. A critical analysis of deployed QKD use cases demonstrates this is a fundamental architectural constraint, not a solvable engineering problem.
Lack of Authentication: QKD solves key distribution but cannot verify the identity of the transmitting party, requiring supplementary classical PKI that itself becomes a quantum vulnerability.
The U.S. National Security Agency explicitly rejects QKD for securing national security networks. QKD will not replace post-quantum cryptography for enterprise and critical infrastructure deployments.
The Superiority of Software-Defined PQC
Post-Quantum Cryptography relies on advanced mathematical structures — primarily lattice-based problems — demonstrably resistant to both classical and quantum computational attacks. In August 2024, NIST finalised three PQC standards: ML-KEM (FIPS 203), ML-DSA (FIPS 204), and SLH-DSA (FIPS 205). Enterprise migration to post-quantum cryptography is now a well-documented transition pathway with established tooling, deployable over existing Ethernet, Wi-Fi, 4G LTE, and serial-bridged legacy OT networks — with no photonic hardware, no dark fibre, and no distance constraints.
VeilNet integrates ML-KEM-1024 for key encapsulation and ML-DSA-256 for packet-level authentication — both at 256-bit equivalent security — directly into its network layer. Every packet traversing a VeilNet-protected OT network is quantum-resistant, regardless of the underlying protocol, without any modification to the PLC firmware or SCADA software running above it.
What Your Existing Security Tools Cannot Do
You may already have Dragos, Claroty, Nozomi, or Xage deployed. These are sophisticated platforms that provide genuine value. But none of them solve the 2028 problem for your legacy OT devices — and understanding why matters for your compliance planning.
Dragos provides exceptional ICS threat intelligence and passive monitoring via deep packet inspection. It sees everything happening on your network. It cannot change anything about how that network authenticates traffic, and it has no path to quantum-resistant key exchange for the legacy devices it monitors. Dragos tells you what is happening. It cannot enforce what is allowed.
Nozomi Networks provides AI-driven asset intelligence and network topology mapping. Like Dragos, its strength is visibility. It does not replace the network layer and cannot enforce PQC natively across OT protocols. Knowing your assets are vulnerable is not the same as making them quantum-resistant.
Claroty's Secure Remote Access solution tunnels connections to OT resources through a zero-trust gateway. However, once the tunnel is established, all traffic within it is implicitly trusted. A compromised endpoint inherits full tunnel access. The tunnelling protocol itself remains classically encrypted. Claroty narrows the perimeter; it does not eliminate the attack surface within it.
Xage Security uses a distributed, identity-based mesh to enforce zero-trust access at the device level — conceptually the closest to VeilNet among current vendors. However, Xage's identity mesh relies on application-layer certificate management and does not address the quantum vulnerability of its underlying transport. A review of top zero-trust solutions for OT environments confirms that no current vendor addresses PQC at the network layer.
The architectural constraint these vendors share is their reliance on the TCP/IP stack. Firewalls, overlay VPNs, and passive monitors attempt to secure a network architecture whose foundational assumptions — that IP addresses represent trusted endpoints, that TLS handshakes performed once protect the entire session — are precisely the assumptions quantum computing invalidates.
Legacy OT protocols compound this further. Modbus has no built-in authentication. OPC-UA Classic relies on X.509 certificates over classical TLS. DNP3 Secure Authentication v5 uses HMAC-SHA-256, whose key exchange is quantum-vulnerable. None of these protocols have a quantum-resistant upgrade path at the protocol layer. The only viable solution is to quantum-resist the network layer beneath them — which is what VeilNet does.
Phase 0: The Current Approach and Its Structural Limits
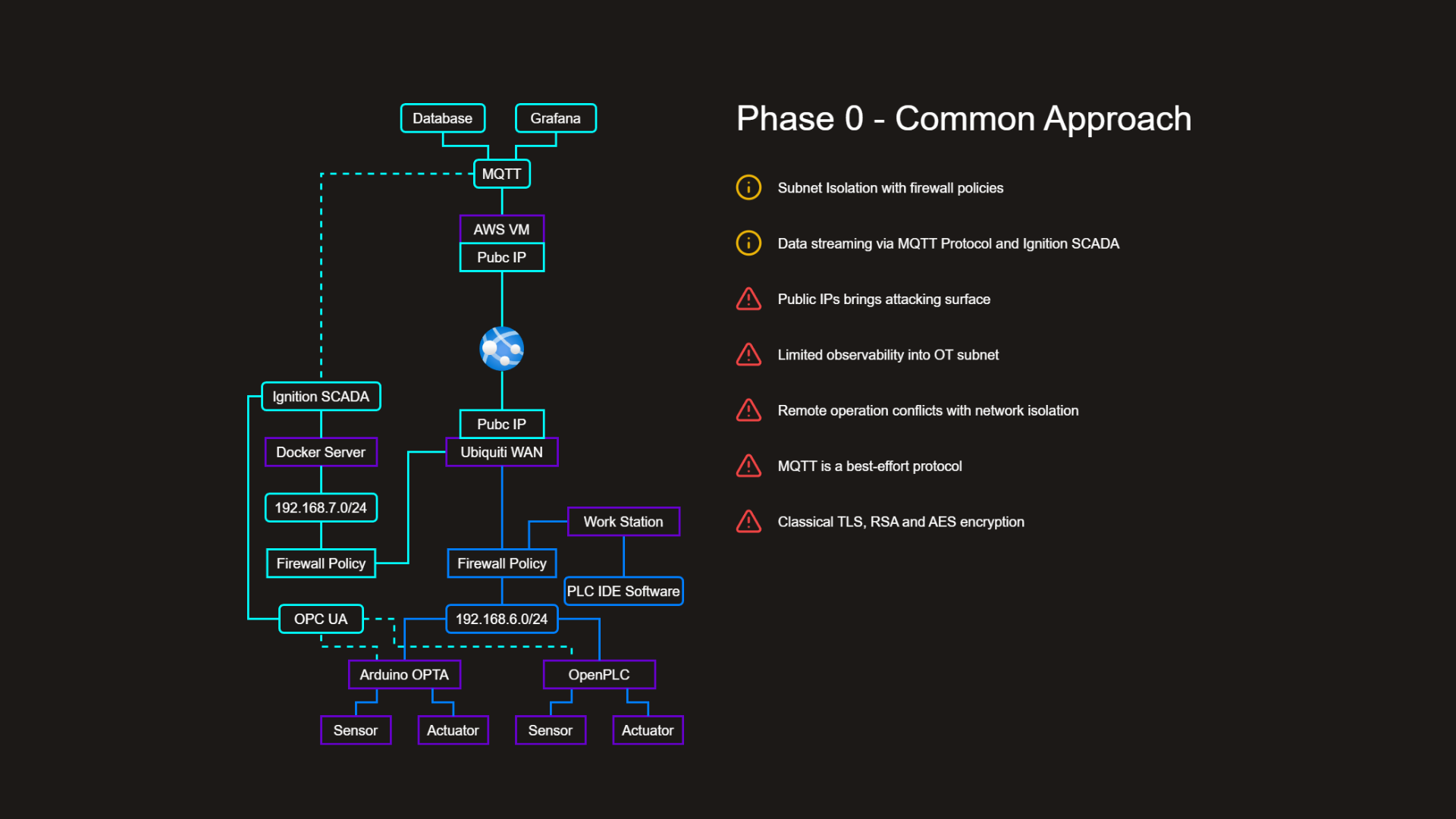
The current industry-standard architecture for OT modernisation bridges the air gap between legacy PLCs and cloud platforms through subnet isolation, MQTT data streaming, and perimeter firewall policies. A representative deployment includes Arduino OPTA and OpenPLC controllers on an isolated 192.168.6.0/24 OT subnet, communicating via OPC-UA to an Ignition SCADA system on a separate 192.168.7.0/24 subnet, with MQTT brokering data upstream through a Ubiquiti WAN to an AWS virtual machine with a public IP, feeding Grafana dashboards and a historian database.
This architecture represents genuine progress over fully isolated legacy environments. It also has structural vulnerabilities that no firewall policy can eliminate:
Public IPs create a permanent attack surface. The AWS VM public IP is reachable on the global internet. Any unpatched CVE or zero-day in the MQTT broker is directly exploitable.
MQTT is best-effort. Message loss during network instability is a production risk for process-critical telemetry. The broker is a single point of failure that the process cannot tolerate.
Remote operation and network isolation are mutually exclusive. Enabling remote engineering access requires opening holes in the same firewall policies that provide OT subnet isolation. Every remote access event is a trade-off against security posture.
Observability stops at the subnet boundary. Firewall-segmented subnets prevent unified monitoring, forcing operators to manage separate visibility tooling for IT and OT.
All encryption is classically vulnerable. Every packet captured today by an adversary is decryptable once a Cryptographically Relevant Quantum Computer exists.
Phase 1: VeilNet Network Replacement
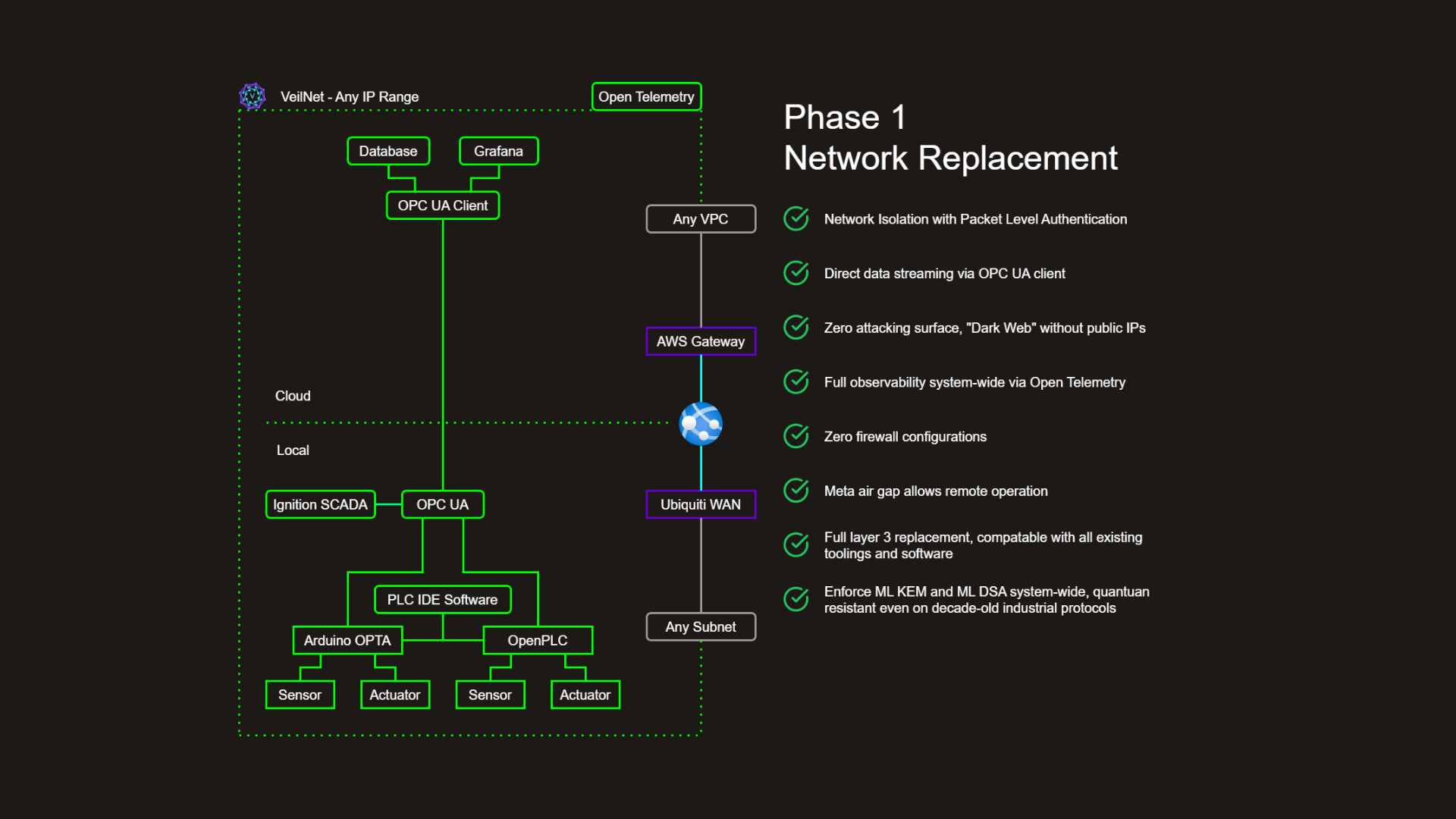
Phase 1 replaces the IP network layer entirely, eliminating every structural limitation above without modifying the Ignition SCADA software, PLC runtime, OPC-UA configuration, or Grafana dashboards running above it. The entire deployment — Arduino OPTA, OpenPLC, Ignition SCADA, PLC IDE workstations, the Ubiquiti WAN uplink, AWS gateway, and cloud historian — is wrapped within a single cryptographically authenticated overlay that operates across any IP range and any subnet boundary.
Network isolation with packet-level authentication. Every packet is authenticated via ML-DSA-256 before the receiving host's network stack processes it. There are no trusted tunnel interiors. A compromised node cannot communicate with protected devices.
Direct OPC-UA streaming. MQTT is eliminated. OPC-UA client connections stream directly from the OT subnet to the cloud historian with guaranteed delivery and no broker single point of failure.
Zero public IP exposure. The AWS gateway has no public IP. VeilNet nodes initiate outbound connections only — no inbound ports open anywhere. The network is invisible to port scanners and unreachable to unsolicited connections.
Full system-wide observability via OpenTelemetry. Unified instrumentation across IT and OT domains without firewall policy exceptions.
Zero firewall configuration. Policy is enforced cryptographically. Firewall rules cannot be misconfigured because they do not exist.
Remote operation without isolation trade-off. The meta air gap enables full bidirectional remote access without opening any physical firewall — stronger isolation than a physical air gap with full connectivity.
Quantum-resistant across all legacy protocols. Modbus, OPC-UA, and DNP3 communications traverse the VeilNet fabric and become quantum-resistant without any protocol-level modification.
The VeilNet Meta Air Gap: Architecture
To achieve true zero-trust security and quantum resistance, the underlying network must be entirely replaced — not monitored or overlaid. VeilNet severs the network stack from the host operating system's kernel itself.
The Anchor Protocol and Linear Scalability
Traditional mesh VPNs scale as O(n²): at 1,000 OT nodes, a full mesh theoretically requires 500,000 concurrent connections. VeilNet's proprietary Anchor Protocol constructs secure data channels entirely on demand and dissolves them when idle. Nodes do not download global routing tables or static peer lists. Route discovery is driven by a Multi-Agent Reinforcement Learning algorithm that models routing as a Markov Decision Process. The result is O(1) linear scalability: the 1,000th OT node costs the same to add as the 10th. The network self-heals from node failures automatically without operator intervention.
The Meta Air Gap via gVisor and Network Namespacing
VeilNet severs the network stack from the host OS kernel by integrating Linux network namespacing with gVisor sandboxing. gVisor is an application kernel written in Go that intercepts all system calls and handles them within its own isolated user-space kernel — the Sentry — before passing only safe, validated operations to the host. VeilNet generates a dedicated network namespace and instantiates an isolated TUN device exclusively within it, connected directly to the VeilNet Conflux process. The host machine's physical network interface is never exposed to application-layer traffic. If a sophisticated exploit targets a network protocol vulnerability, the attack is permanently trapped within the gVisor sandbox. The host machine, the hypervisor, and the physical OT network remain completely unaffected.
IP addressing and name resolution are handled without any centralised dependency. Each Conflux node derives its address cryptographically from its post-quantum identity key, and DNS resolution is embedded within the node's Virtual Kernel. There is no central DHCP server to fail, and no central DNS resolver to become a chokepoint or attack surface. Name resolution remains available even during partial network partitions — a critical property for process control environments where a single infrastructure failure must not cascade into a process outage.
Phase 2: Self-Healing "PLC" Edge Cloud
Phase 1 secures the network. Phase 2 eliminates the second class of failure that no network security tool can address: the hardware-bound PLC itself. In every conventional OT deployment, the PLC is a single point of failure with no software-defined recovery path. When it fails, the process stops. When the vendor discontinues the hardware, the process is stranded. When a logic update is required, the process must be halted. These are not edge cases — they are the normal operating conditions of OT infrastructure, and they carry direct financial consequences measured in thousands of dollars per minute of unplanned downtime.
Phase 2 changes the fundamental assumption. Rather than treating the PLC as an inseparable combination of hardware and logic, VeilNet decouples the two. Control logic becomes a portable, version-controlled software workload that the cluster can schedule on any available node, update without halting the process, and recover automatically from any hardware failure — with full state preserved. The hardware underneath becomes interchangeable. The process becomes resilient.
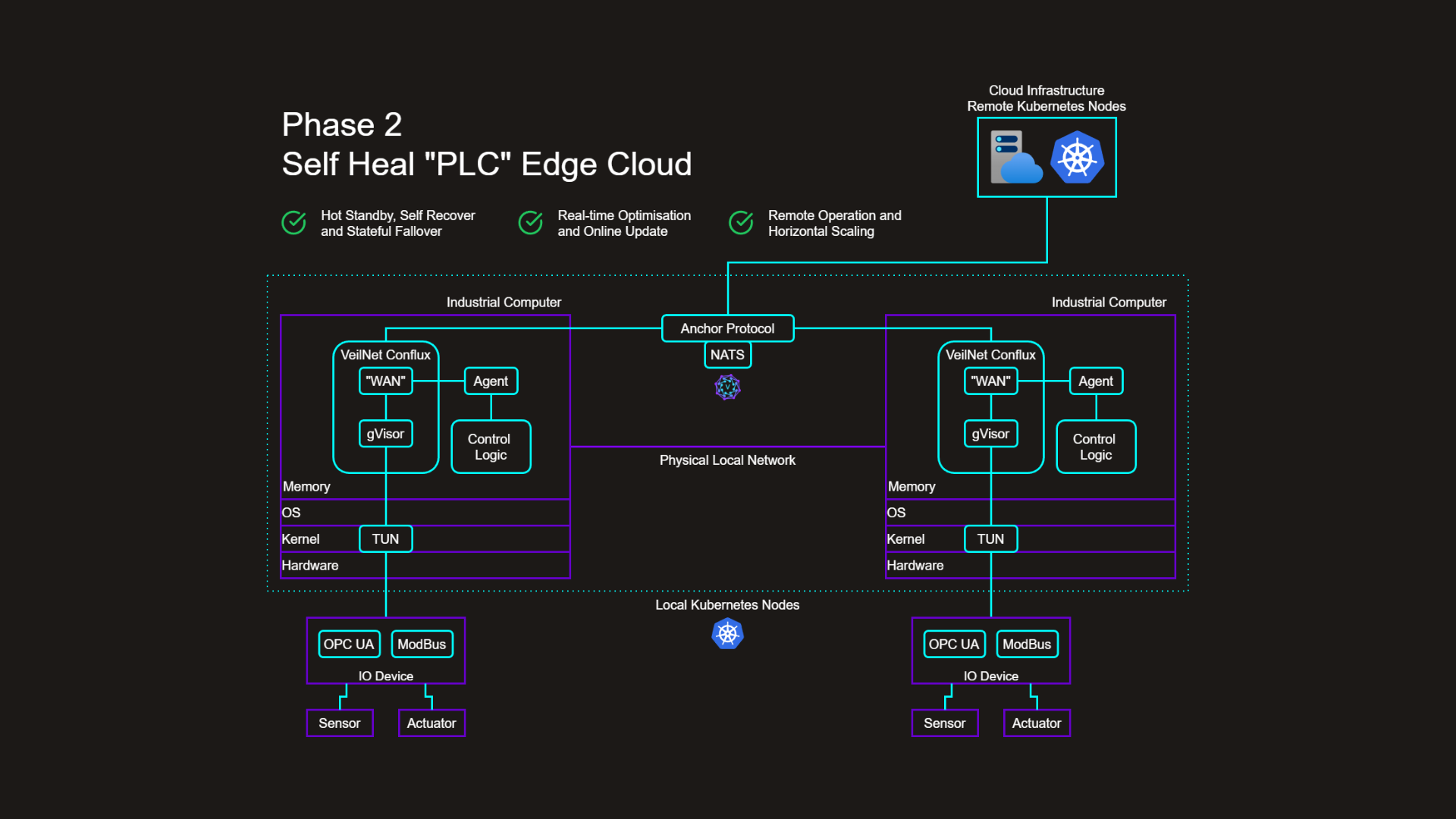
Phase 2 elevates VeilNet Conflux from a network node into a full industrial compute runtime. PLC logic migrates into containerised workloads orchestrated across a multi-site Kubernetes cluster spanning local edge hardware and cloud infrastructure.
Each industrial computer hosts a VeilNet Conflux instance with four integrated components: a virtual WAN module backed by gVisor for host-kernel isolation, a Conflux Agent managing IO device communication and cluster coordination, a Control Logic container running the encapsulated PLC program, and a TUN interface at the kernel boundary enforcing packet-level ML-DSA authentication on every IO device communication.
Virtual WAN: Identity-Authenticated IO Device Communication
The Conflux virtual WAN creates a local network boundary between the Agent and the physical IO devices. Every OPC-UA read or Modbus write passes through the TUN interface and is authenticated with ML-DSA-256 before delivery. No process on the industrial computer can communicate with a physical IO device without a valid Dilithium signature — not even a process running on the same machine. This applies identity-based enforcement within the local computer itself, not just across the wide area network.
Local Real-Time Control: Agent-Driven Coordination
Within each industrial computer, the Conflux Agent manages all IO device communication and provides the local coordination interface for the Control Logic container. IO device telemetry is ingested and made available to the Control Logic container via the Agent's local interface. The Control Logic executes its algorithms against the received telemetry and delivers actuation commands back through the Agent to the appropriate IO devices. OPC-UA connections to local IO devices are handled directly by the Agent, preserving control loop latency without routing telemetry through the wide area network. The Control Logic container has no direct access to the network or to IO devices — all communication passes through the authenticated Agent interface.
Stateful Coordination and Cross-Site Control
The Anchor Protocol governs VeilNet's network layer — packet routing, identity authentication, and self-healing path selection. The control plane operates through the Conflux Agents themselves. Each Agent is not merely a local IO broker; it is an active participant in a distributed coordination fabric. Agents continuously replicate control state, telemetry, and command streams across the cluster before any state change is committed. Where the Anchor Protocol ensures that packets between nodes are authenticated and routed resiliently, the Agents ensure that the process state is never lost — regardless of which physical node the Control Logic is executing on.
If the primary host suffers a hardware failure, a replica Agent assumes coordination from the exact last committed state with zero data loss and zero manual intervention. This mathematically guarantees near-zero MTTR for any process control workload on the VeilNet fabric. The guarantee is structural — it derives from how Agents manage distributed state across the cluster, not from the operational practices of the maintenance team.
This coordination model extends transparently across site boundaries. Agents on geographically separated industrial computers communicate over the Anchor Protocol's authenticated overlay, presenting a unified control surface to their respective Control Logic containers. An Agent on one industrial computer can coordinate with IO devices connected to a second machine, enabling joint control logic across physically separated hardware. Cross-site control architectures that require PLC hardware co-location today — because coordination over classical networks is unpredictable — become achievable across any topology connected by the VeilNet fabric. The Anchor Protocol's self-healing routing ensures the coordination channel itself remains resilient to individual node and link failures without operator intervention.
Overcoming the Limitations of ROS 2 in Multi-Host Real-Time Control
For advanced manufacturing and robotics environments considering ROS 2 as control middleware, VeilNet's Anchor Protocol-driven architecture provides a stronger alternative. ROS 2 introduces significant challenges in multi-host, process-critical deployments.
ROS 2's DDS middleware relies on UDP multicast for node discovery and message distribution. In a multi-subnet OT environment, DDS multicast either fails to traverse subnet boundaries or must be explicitly forwarded, negating network isolation. ROS 2 also suffers from scheduling unpredictability in multi-host deployments — including priority inversion during callback execution — that prevents reliable, deterministic task execution in process-critical environments. And ROS 2 nodes are generally stateless: a crashed control loop loses its state entirely.
VeilNet's Anchor Protocol resolves all three problems. There is no multicast dependency — coordination traverses the authenticated VeilNet overlay regardless of subnet topology. Control loop timing is deterministic at the microsecond level, enforced by the Agents rather than by middleware scheduling. And control state is continuously replicated across the cluster, ensuring that any node failure results in automatic resumption from the last committed state with zero data loss.
Kubernetes in OT: An Emerging Industry Consensus
The containerisation of industrial control logic is not speculative. OMRON, one of the world's largest PLC manufacturers, selected Red Hat OpenShift as the model for its virtualised control platform proof-of-concept, explicitly targeting remote operation of industrial control equipment from containers. VMware, ZEDEDA, and Kubermatic all converge on the same conclusion: given the scale of hardware spread across industrial sites, standardisation and automation enabled by cloud-native technologies are the only viable ways to manage distributed OT systems. Half of enterprise Kubernetes adopters now run production clusters at the edge.
For resource-constrained industrial computers, K3s — packaged as a single binary under 100MB — is optimised for edge and IoT environments. RKE2, its enterprise-grade counterpart, provides CIS Kubernetes Benchmark hardening by default and supports FIPS 140-2 compliance — directly relevant to ASD CI Fortify aligned deployments. Many organisations run K3s at the edge and RKE2 in the data centre or cloud, managed from a unified control plane — precisely the topology VeilNet Phase 2 supports.
The Unsolved Networking Problem in Multi-Site Kubernetes
The principal obstacle to multi-site Kubernetes deployments in OT is not the orchestration layer — it is the network. Kubernetes is not designed for easy cross-cluster service discovery. Standard approaches using load balancers eliminate identity-aware security, increase attack surface, and add routing complexity. Multi-region deployments require cloud-provider-specific interconnects — AWS Direct Connect, Azure ExpressRoute — that introduce classical TLS tunnels, centralised chokepoints, and no path to quantum-resistant key exchange. Service meshes such as Istio or Linkerd add their own operational overhead and certificate management without addressing PQC.
VeilNet resolves this at the root. Kubernetes nodes at geographically separated industrial sites and cloud regions join a single cluster over the VeilNet fabric — without public IP exposure, without service mesh overhead, and without cloud-provider interconnect dependencies. Pod-to-pod communication across site boundaries is authenticated with ML-DSA-256. No load balancer. No external DNS record. No classical TLS tunnel interior to laterally traverse.
Multi-Site Cluster: Dynamic Allocation and Self-Recovery
Within this cluster, Control Logic containers are standard Kubernetes workloads, scheduled dynamically across available nodes. This delivers four capabilities unachievable with hardware-bound PLCs:
Hot standby and stateful failover. If the active PLC host fails, Kubernetes reschedules the workload and the Anchor Protocol's distributed state replication ensures the replacement resumes from the exact last committed state with zero data loss.
Zero-downtime logic updates. Kubernetes rolling updates replace PLC logic while the process continues, inheriting full process state from the predecessor via the Agents' replicated state.
Remote operation and horizontal scaling. Cloud Kubernetes nodes extend the cluster beyond the physical site. New industrial sites join the existing cluster and immediately inherit all security, monitoring, and failover capabilities.
On-demand dynamic allocation. Control Logic migrates between edge and cloud nodes in response to load and maintenance requirements, with process continuity preserved throughout by the Agents' replicated state guarantees.
Direct Business Impacts and Operational Synergies
Infrastructure Consolidation and CapEx Reduction
Legacy OT security requires purchasing, licensing, deploying, and maintaining separate hardware for physical firewalls, intrusion detection systems, VPN concentrators, SCADA data historians, remote access gateways, and network monitoring platforms. VeilNet's software-defined network replacement consolidates these into a single logical layer. Firewall rules are replaced by cryptographic packet-level authentication. VPN infrastructure is eliminated. Remote access gateways are replaced by the meta air gap fabric. The cost reduction is structural — it compounds over the entire maintenance lifecycle, not just the initial deployment.
Mitigating Regulatory Risk and Personal Liability
The financial penalties for failing to meet ASD 2028 requirements under the enhanced SOCI Act CIRMP Rules are severe. Critically, responsible officers of SOCI-registered entities face personal liability exposure — not just organisational penalties. The ASD CI Fortify program treats quantum-readiness as a baseline requirement, and CI Fortify alignment is increasingly expected by insurers underwriting critical infrastructure cyber risk policies.
VeilNet provides a direct, auditable evidence trail demonstrating NIST FIPS 203 and FIPS 204 compliance across the entire OT network. Every packet is authenticated with ML-DSA-256. Every key exchange uses ML-KEM-1024. This compliance applies automatically to Modbus, OPC-UA, DNP3, and every other protocol running above VeilNet — without separate compliance tooling per system.
Maximising Uptime and Reducing MTTR
In manufacturing and critical infrastructure, unplanned downtime costs between $50,000 and $250,000 per hour across typical heavy industry deployments. Traditional PLC hardware failures require physical replacement, firmware restoration, and manual process state reconstruction — an MTTR measured in hours or days. VeilNet's self-healing PLC edge cloud reduces this to near-zero. Containerised PLC logic coordinated by the Conflux Agents resumes automatically within seconds of a primary node failure, with no data loss and no manual intervention. Combined with VeilNet's self-healing MARL routing — which autonomously reroutes around failed network paths — the architecture provides defence-in-depth resilience at both network and application layers.
Recognising the Human Challenge: The Path to Partnership
VeilNet is direct about what Phase 2 requires of OT organisations. This is not a configuration change — it is a fundamental shift in how industrial control systems are conceived, programmed, deployed, and maintained. We believe the shift is necessary and achievable. We also believe that underestimating its human dimensions would be a disservice.
The Weight of Ladder Logic
Ladder logic has been the dominant language of industrial control for over five decades, and its longevity is not an accident. When the first generation of PLCs replaced hardwired relay panels, ladder logic was deliberately designed to mirror relay circuit diagrams so that maintenance technicians could own it without software training. That design decision made it extraordinarily durable. The control program is not just owned by automation engineers — it is maintained by electricians and floor supervisors who troubleshoot it during unplanned shutdowns, often without any formal programming background.
The containerised, Anchor Protocol-driven model VeilNet introduces uses general-purpose languages — Go, Python, Rust — packaged as OCI containers, orchestrated by Kubernetes, and debugged through distributed tracing tools. These are software engineering competencies largely foreign to the OT workforce. McKinsey's research identifies manufacturing as among the sectors where the reskilling challenge will be most acute. The World Economic Forum estimates 50% of all employees will need reskilling due to technology adoption, with two-thirds of current job skills changing within five years. Modular, stackable learning paths that fit within production schedules — not extended off-site programmes — are the only format that works for OT engineers who cannot suspend operations to retrain.
What Is Not Being Retired
Phase 2 does not require the retirement of existing PLC hardware, IO wiring, sensor and actuator infrastructure, or the process knowledge OT engineers have built over careers. The OPC-UA and Modbus protocols remain unchanged. The control logic itself — interlock conditions, PID loops, sequence logic — migrates from vendor-specific ladder diagram files to containerised programs, preserving the same logical behaviour while gaining portability, version control, and stateful resilience.
The transition is analogous to the original move from hardwired relay panels to PLCs: the control philosophy survives; the medium changes. That transition also took decades, site by site, as equipment reached end of life. VeilNet anticipates the same incremental trajectory. Phase 1 delivers immediate, standalone value without changing any PLC programming practice. Phase 2 is an optional, additive step adopted progressively, beginning with new installations where the installed base constraint is lowest.
We Are Seeking Partners for This Journey
Phase 2 represents a direction the OT industry is already moving in — OMRON's OpenShift PoC, ZEDEDA's edge Kubernetes platform, and the growing body of research on containerised industrial control all confirm the direction. VeilNet provides the secure, quantum-resistant network fabric that makes it operationally viable. But the journey requires partners who bring what VeilNet does not: deep OT domain expertise, established relationships with process engineers, curriculum development capability, and the operational credibility to guide organisations through a transformation of this magnitude.
We are seeking partners across three categories. System integrators and automation engineering consultancies with existing OT customer relationships, who can identify sites and workloads where Phase 2 adoption is technically appropriate and commercially motivated. Industrial training providers and vocational education institutions with the curriculum infrastructure to develop upskilling programmes bridging OT control engineering and cloud-native software development, designed around production schedules. And hardware and platform partners — PLC manufacturers, industrial PC vendors, edge computing platform providers — with whom VeilNet can co-develop reference architectures, certified integration profiles, and validated deployment patterns that reduce the integration burden on end customers.
This is not a change that will happen overnight. We do not expect it to. What we are asking of partners is a shared conviction that the direction is right, and a willingness to take the first steps together.
Conclusion
The OT industry faces two converging challenges. The first is structural: hardware-bound PLC logic creates operational fragility that costs hours of downtime per incident, blocks zero-downtime updates, and cannot scale without capital expenditure. The second is existential: the ASD's 2028 quantum-readiness deadline is not aspirational guidance — it is an enforceable obligation that responsible officers of SOCI Act registered entities face personally. Hardware replacement cannot address either challenge at the required pace.
VeilNet addresses both from a single software-defined deployment. Phase 1 replaces the network layer, delivering quantum-resistant connectivity, zero public IP exposure, remote operation without firewall compromise, and full OT protocol coverage — without touching a single PLC, SCADA configuration, or IO device. Phase 2 replaces the control plane, delivering self-healing PLC failover, zero-downtime logic updates, and dynamic cross-site allocation across a multi-site Kubernetes cluster coordinated by the Anchor Protocol — adopted incrementally, at the pace each organisation can manage.
The technical debt accumulated over decades of Purdue-model infrastructure cannot be resolved by adding monitoring layers above it. It requires replacing the foundation. VeilNet is that replacement.
VeilNet - The Future-Ready Zero Trust Network Architecture
How VeilNet delivers quantum-safe security, linear scalability, and cost reduction while eliminating network complexity for both AI-driven and traditional enterprise environments.
Defeating the Security Risks of Autonomous AI Agents with Post Quantum Zero Trust
Learn how VeilNet secures the autonomous enterprise against AI agent risks using Conflux post-quantum networking and Aether data plane orchestration.